- Main
- Computers - Networking
- The Practice of Network Security...

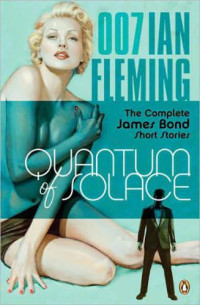
The Practice of Network Security Monitoring: Understanding Incident Detection and Response
Richard BejtlichQuanto ti piace questo libro?
Qual è la qualità del file?
Scarica il libro per la valutazione della qualità
Qual è la qualità dei file scaricati?
Network security is not simply about building impenetrable walls—determined attackers will eventually overcome traditional defenses. The most effective computer security strategies integrate network security monitoring (NSM): the collection and analysis of data to help you detect and respond to intrusions.
In The Practice of Network Security Monitoring, Mandiant CSO Richard Bejtlich shows you how to use NSM to add a robust layer of protection around your networks—no prior experience required. To help you avoid costly and inflexible solutions, he teaches you how to deploy, build, and run an NSM operation using open source software and vendor-neutral tools.
You'll learn how to:
• Determine where to deploy NSM platforms, and size them for the monitored networks
• Deploy stand-alone or distributed NSM installations
• Use command line and graphical packet analysis tools, and NSM consoles
• Interpret network evidence from server-side and client-side intrusions
• Integrate threat intelligence into NSM software to identify sophisticated adversaries
There’s no foolproof way to keep attackers out of your network. But when they get in, you’ll be prepared. The Practice of Network Security Monitoring will show you how to build a security net to detect, contain, and control them. Attacks are inevitable, but losing sensitive data shouldn't be.
In The Practice of Network Security Monitoring, Mandiant CSO Richard Bejtlich shows you how to use NSM to add a robust layer of protection around your networks—no prior experience required. To help you avoid costly and inflexible solutions, he teaches you how to deploy, build, and run an NSM operation using open source software and vendor-neutral tools.
You'll learn how to:
• Determine where to deploy NSM platforms, and size them for the monitored networks
• Deploy stand-alone or distributed NSM installations
• Use command line and graphical packet analysis tools, and NSM consoles
• Interpret network evidence from server-side and client-side intrusions
• Integrate threat intelligence into NSM software to identify sophisticated adversaries
There’s no foolproof way to keep attackers out of your network. But when they get in, you’ll be prepared. The Practice of Network Security Monitoring will show you how to build a security net to detect, contain, and control them. Attacks are inevitable, but losing sensitive data shouldn't be.
Categorie:
Anno:
2013
Edizione:
1
Casa editrice:
No Starch Press
Lingua:
english
Pagine:
376
ISBN 10:
1593275099
ISBN 13:
9781593275099
File:
PDF, 17.39 MB
I tuoi tag:
IPFS:
CID , CID Blake2b
english, 2013
Leggi Online
- Scaricare
- pdf 17.39 MB Current page
- Checking other formats...
- Convertire a
- Sbloccare file di conversione di dimensioni maggiori di 8 MB Premium
Il file verrà inviato al tuo indirizzo email. Ci vogliono fino a 1-5 minuti prima di riceverlo.
Entro 1-5 minuti il file verrà consegnato al tuo account Telegram.
Attenzione: assicurati di aver collegato il tuo account al bot Z-Library Telegram.
Entro 1-5 minuti il file verrà consegnato al tuo dispositivo Kindle.
Nota: devi verificare ogni libro che desideri inviare al tuo Kindle. Controlla la tua casella di posta per l'e-mail di verifica da Amazon Kindle Support.
La conversione in è in corso
La conversione in non è riuscita
Vantaggi dello status Premium
- Inviare a lettori di e-book
- Limite aumentato di download
 Converti i file
Converti i file Più risultati di ricerca
Più risultati di ricerca Altri vantaggi
Altri vantaggi
Termini più frequenti
Liste di libri correlati

































































































































































 Amazon
Amazon  Barnes & Noble
Barnes & Noble  Bookshop.org
Bookshop.org